WPA2 is a certification program maintained by IEEE that oversees standards for security over wireless networks. Web browsers and server operate at the application layer.
Initially WEP was expected to offer the same security level for wireless networks as wired networks do however there are a lot of well-known issues in WEP which are easy to exploit.

. The encryption method is commonly referred to as CCMPAES. The WPA protocol implements much of the IEEE 80211i standard. WEP used a 64-bit or 128-bit encryption key that must be manually entered on wireless access points and devices and does not change.
WPA3-Personal uses CCMP-128 and AES-128. Temporal Key Integrity Protocol was a stopgap security protocol used in the IEEE 80211 wireless networking standard. Changes key every 10000 data packets sent.
The AES encrypts and decrypts data in blocks of 128 bits 16 bytes and can use keys of 128 bits 192 bits and 256 bits. WEP used a 64-bit or 128-bit encryption key that must be manually entered on wireless access points and. AES uses a 128- bit key and encrypts data in 128- bit blocks.
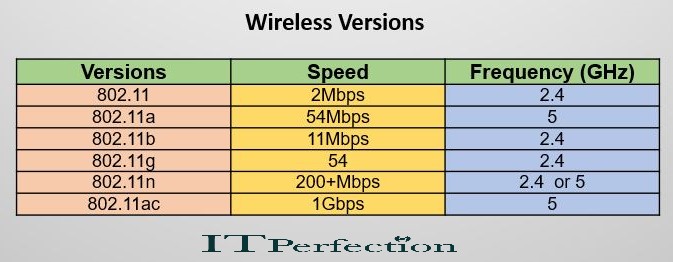
WPA3-Enterprise has optional 192-bit security encryption and a 48-bit IV for heightened protection of sensitive corporate financial and governmental data. Understanding wireless networking and encryption standards 80211 abgn. To use a wireless key on a home network an administrator must first enable a security method on the broadband router.
It uses various Extensible Authentication Protocol EAP for authenticating various categories of network users. CCMPAES uses several enhancements including temporal keys TK packet numbers PN nonce number or bit string used only once upper layer encryption and additional authentication data AAD. Which field describes the version of 80211 that is being used.
Unfortunately however both WEP 64 nor WEP 128 are vulnerable to various exploits so its recommended that you use a different security standard for your small businesss Wi-Fi. Which wireless security standards uses a 128-bit key. Which wireless security standards and certfications call for the use of ccmpaes encryption.
WPA-PSK WPA Pre - Shared Key It was developed for use in home and small offices and does not need any authentication server. The former uses a 64-bit key whereas the latter uses a 128-bit key. Keys with longer length 128 bit or above are almost unbreakable since it takes several to couple of hundred years to break them with the modern.
Wired Equivalent Privacy WEP. An 80211 frame contains a number of fields. WEP used a 64-bit or 128-bit encryption key that must be manually entered on wireless access points and devices and does not change.
CCMPAES uses several enhancementsincluding temporal keys TKpacket numbers PNnonce number or bit string used only onceupper layer encryptionand additional authentication data AAD. AES uses a 128-bit key and encrypts data in 128-bit blocks. What three main components constitute an 8021xeap framework.
128 bit temporal key message integrity check 48-bit IV. CCMPAES uses several enhancements including temporal keys TK packet numbers PN nonce number or bit string used only once upper layer encryption and additional authentication data AAD. Specifically the Temporal Key Integrity Protocol TKIP was adopted for WPA.
Which wireless standard uses a 128-bit key. Wi-Fi Protected Access WPA Another common and widely used. Which wireless security standards uses a 128-bit key.
There are WEP WPA WPA2 and WPA3 wireless security protocols. What is WPA WPA2 PSK security. The higher the length the better.
Of those two options WEP is 128 is more secure. Which wireless security standards uses a 128-bit key. It also increases the authentication encryption to 256-bit and the key encryption to 384-bit.
Around the time of WEP US. Which type provide speeds above 1544 megabits per second. Hence it provided some more security to the data that was.
IEEE Std 80211i. TKIP was designed to replace WEP. 128-bit WEP encryption uses a user-provided static key of what size.
It also standardizes the 128-bit cryptographic suite and disallows obsolete security protocols. Provides better security than WEP WPA uses temporal key Intergrity Protocol or TKIP which includes a number of features aimed at addressing vulnerabilities in WEP. But there were some specific weaknesses which were found with this protocol.
Using Wireless Keys. Wireless standard that generates a changing 128-bit per packet security key. The original flawed wireless security protocol is known as.
TKIP temporal key Intergrity protocol uses a 128-bit encryption key and a 48-bit initialization vector. The encryption method is commonly referred to as CCMPAES. This proved problematic for WEP.
It uses the Temporal Key Integrity Protocol TKIP which provides a 128-bit encryption key. WPA3-Enterprise with 192-bit Mode provides the option for minimum 192-bit encryption instead of 128-bit. WPA system Every networked device needs a gateway to know where to send network intended for outside of the local network segment.
AES uses a 128- bit key and encrypts data in 128- bit blocks. Among these WPA2-AES should be used whenever possible. WEP Wired Equivalent Privacy was approved as a Wi-Fi security standard in September 1999.
The strength of the key depends on its length. WPA WEP and other popular encryption types and their features. It requires a complicated setup and provides automatic key generation and additional security measures.
The WPA protocol implements the Temporal Key Integrity Protocol TKIP. TKIP employs a per-packet key meaning that it dynamically generates a new 128-bit key for each packet and thus prevents the types of attacks that compromised WEP. One was the 128 bit and the other was the 64 bit key.
In other words your key length can be anything between 128 0s to 128 1s. Home routers offer a choice among multiple options usually including. Which of these security standards provides very weak security.
Government restrictions on the export of cryptographic technology caused access point manufacturers to limit their devices to 64-bit encryption. Though this was later lifted to 128-bit even this form of encryption offered a very limited possible key size. Remember that higher the length of the key the better your message is protected.

Wifi Encryption Demystified Bmp 1200 927 Cybersecurity Infographic Computer Network Computer Programming
![]()
Wpa Vs Wpa2 Which Wifi Security Should You Use

Wpa Vs Wpa2 Which Wifi Security Should You Use
Wireless Networks Security Cissp Exam Itperfection Network Security
0 Comments